Just when you thought Liam Neeson has kept your world safer, a sequel to Taken 2 may have been happening already right in front of your computer screen.
If you experienced logging into your computer and instead of the normal booting process a warning message pops up saying that you have been restricted access to your own computer, then your computer has just become the new character in Taken 3. Seriously.
The message usually appears as if it is coming from a cybercriminal enforcement agency as a warning that you have transmitted illegal or inappropriate information. There will also be a message telling you that your computer will remain encrypted and locked until you agree that you pay a certain reactivation fee or “ransom” so you can access your computer again.
But the truth is, it’s not a message from the NBI or FBI. It’s a type of malware that you yourself have inflicted upon your poor granny old Windows 7 laptop.
This malware attack is commonly called “Ransomware,” otherwise known as crypto-virus or crypto-trojan. This type of malware infects your computer system just like a typical computer worm does. This usually happens when the malware identifies weaknesses points in your network or anti-virus software. Another reason is when an unknown file has been downloaded by a user.
When the ransomware has gain accessed to your system, it will start to encrypt personal files like financial data on the hard drive. This provides the ransomware-maker the decryption key necessary to regain use of an attacked computer. This will be the opportunity for the ransomware-maker to force the computer owner or user to either buy a special “program” to decrypt the files or sometimes even ask for a Paypal payment. In most cases when the computer owner refuses to buy the program or pay a fee, un-encrypting the attacked files is almost impossible.
How To Prevent and What To Do In Case of Attack
1) Bring your computer right away in to be checked and re-formatted by a trusted and experienced computer professional. Be ready to accept the hard truth that all your files and data may all be wiped out.
2) Do not send money to the online scammer.
3) Never give your banking information such as your savings account or routing number.
4) Back up your files regularly on a stand-alone hard disk. Never ever leave your hard disk connected to your laptop or PC.
5) Never save your online investment portfolio or banking facility passwords in your computer. Go old school. Write down on a notebook all the email addresses, passwords, account numbers, and other personal financial data.
Real Life Computer and Data Hostage-Takers
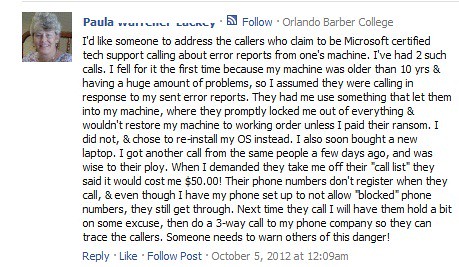
There’s also another variation of this “ransomware” where actual hackers will call you up telling you that they’re from Microsoft and have responded to your sent error reports. Here’s an actual testimonial given to our anti-identity theft organization:
If you have been a victim of hacking or “computer-data-for-ransom” schemes, report immediately to the National Bureau of Investigation (NBI) hotlines (632-525-4093/632-524-6395) if you are in the Philippines or file a complaint at the Federal Bureau of Investigation (FBI) on this website: Internet Crime Complaint Center if you are in the USA.
Always take extra precautions when using your computer. Never abuse it.
Be informed on how to protect your identity by subscribing to BurnGutierrez.Com.
—
Resources:
1) Identity Theft Resource Center
Thanks for sharing this bro. Timely ito. I just had a hack-scare yesterday on my blog account. Good thing, I made sure that basic security measures on account security are on place. Plus, I backup my blog content frequently. Backup is really a must on all our important files.
Everyone’s vulnerable bro. Even those who claim to be the best hacker fighters embarrassingly gets attacked sometimes. It pays to backup files all the time!
A negative thinker see a difficulty in every opportunity
A positive thinker see an opportunity in every difficulty,
wish u an optimistic life..
Good information. now i discussing about.. How to save computer from hackers